Analysis
Sponsored content – Towards a Threat Agnostic Understanding of Child Sexual Exploitation: Group-Based CSE in Complex Networks
By Seth Cooke, i2.
The National Audit on Group-Based Child Sexual Exploitation and Abuse has placed an urgent operational requirement on every constabulary in England and Wales. Recommendation 2(ii) calls for “A review of police and children’s services records to identify children who have been at risk of or harmed by sexual exploitation.” The national inquiry formally begins in April 2026. Operation Beaconport, led by the National Crime Agency, is already reviewing over 1,200 cases referred by 23 police forces.
This article describes how i2 can support agencies seeking to meet these requirements. Our software is already available to every UK constabulary under the BlueLight Commercial Access for All Agreement. Adoption of i2 technology is supported by the Home Office Police Efficiency and Collaboration Programme under the government white paper, From Local to National: A New Model for Policing.
In our previous article, ‘Reigniting Intelligence: Towards a Threat-Agnostic Intelligence Capability’, we described how you can use i2 to modernise intelligence capabilities via a self-determined, self-service model, minimising costs and delivery timescales.
In this article, we demonstrate how you can:
- Automate the identification of CSE risk using your existing software, in alignment with your information governance and your application of academic research.
- Quickly understand group-based CSE, mapping networks of vulnerable children and adult exploiters — providing early intervention and harm prevention opportunities.
- Enrich your understanding via data from other sources such as PND, partners or communications data, to fill intelligence gaps.
- Apply a threat-agnostic approach as a force multiplier to analysis, delivering on the recommendations of the National Intelligence Model Landscape Review.
- Navigate existing pathways to improve partnership ways of working, aligned with the evidence base and ethos of Contextual Safeguarding.
- Achieve insight into the community tensions that can accompany CSE, including how the “grooming gangs” narrative is often exploited on social media.
Child Sexual Exploitation & Group-Based CSE: the i2 Approach
Identifying CSE requires clearly defined terms. The October 2025 HMICFRS Progress Report found that nearly all police forces have adopted the IICSA definition of group-based CSE. i2 recommends identifying CSE risk to children first – then using network analysis to reveal the adult groups that exploit them.
Automate the identification of CSE risk
The Casey Audit advocates for the ‘Smith Algorithm’ as good practice, describing West Yorkshire Police analyst Paul Smith’s approach of identifying children with regular missing episodes, who have been the victim of a sexual crime or described in intelligence relating to sexual activity. Data on multiple vulnerabilities is then used to prioritise those most at risk. i2 software allows suitably trained and authorised analysts to deliver this in a configurable, auditable, explainable, operationalisable manner, aligned with information governance legislation and policy.
You can apply risk weightings defined by strategic terms of reference, recommended by academia, and factors such as those listed in the College of Policing Approved Professional Practice. Relevant datasets may include: crime and non-crime incidents, intelligence, missing person reports, vulnerability risk assessments, flags and warnings — as well as any partnership data for which you have approved access and permission. Results can be accessed in i2 or integrated into platforms such as PowerBI, Qlik, Tableau or Cognos.
Some agencies stop at this stage. That approach carries significant risk. Automated analytics that encourage agencies to act according to a score or quota, without context or wisdom, can be misleading, dehumanising and disproportionate.
Instead, i2 recommends a multiagency public health approach to understanding how CSE risk impacts communities. This is supported by network analysis – which can identify relational risk and networks of adult exploiters.
Quickly understand group-based CSE
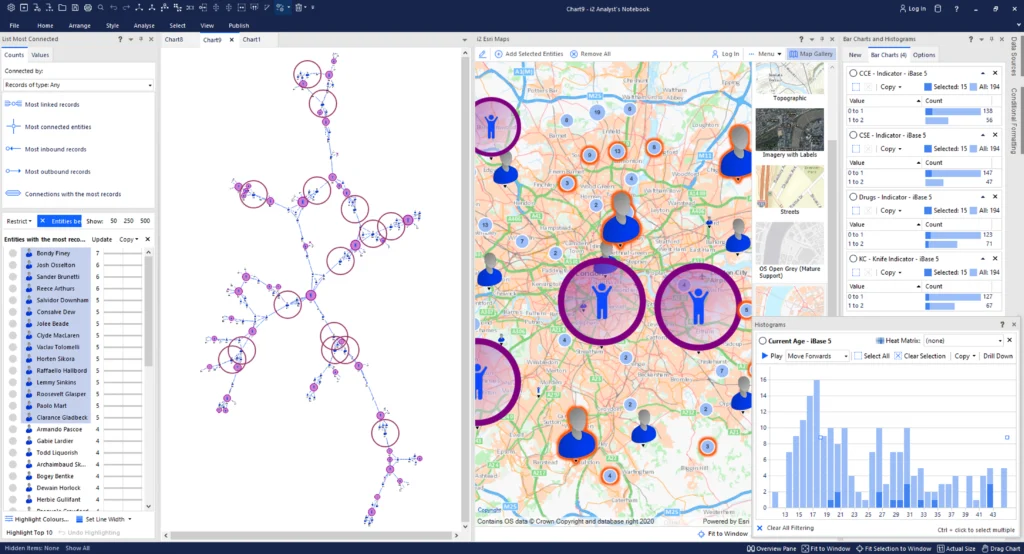
i2 is renowned for network analysis. This is the discipline that lets you intervene early and disrupt with precision by making it quick and simple to map and understand risk across whole interrelated communities.
Many vulnerable children at risk of CSE are likely to know each other, and may have recorded associations with adult exploiters. Tradecraft taught by i2 and our academic partners allows you to quickly identify groups of adult suspects and their roles, such as influencers, facilitators, brokers and gatekeepers. This aligns directly with Casey Recommendation 8, which calls for CSE to be treated as serious and organised crime. Network analysis also delivers proactive intelligence opportunities — to protect emerging cohorts at risk through social proximity, as well as identifying protective factors, community guardians or CHIS who have sight of CSE-linked individuals in their network.
All constabularies already own sufficient data for network analysis. It will reveal many “unknown knowns” — hidden associations that are recorded yet difficult to see using only systems such as Niche or Connect, that become obvious when using i2. Tragically, these associations may also become obvious with hindsight. This is the choice: assess unmet demand by revealing unknown knowns now, or wait until they are revealed during a Serious Case Review. Either way, they are present in the data already.
While all constabularies can begin now, enriching local intelligence with data from national systems and partners fills critical gaps.
Enrich your understanding using data from other sources
i2 provides several tools for matching and merging data from national systems such as PND or NAS, investigative datasets such as communications data, and partnership data from local authorities and schools. When unique child identifiers are introduced nationally, as called for in Casey Recommendation 6, i2’s entity resolution capabilities will allow analysts to match and link records across agencies with greater confidence.
When it comes to existing police data, monthly exports from PND can already be imported to into i2, as well as ad hoc on-demand exports defined by advanced users of PND. This provides essential insight into cross-border risk, including accessing data relating to Organised Crime Groups, County Lines and Modern Slavery & Human Trafficking. For investigative data, i2 Insights can automatically import, standardise and analyse data from NAS and communication service providers. These capabilities are already available to all UK police analysts now — contact us if you want to find out more.
Extending the picture thematically — across all control strategy priorities — is where the approach becomes a genuine force multiplier.
Apply a threat-agnostic approach as a force multiplier to analysis
Many intelligence opportunities will be revealed by applying the same i2 capabilities used to automate CSE to every other Control Strategy thematic. The National Intelligence Model Landscape Review calls this threat-agnosticism — revealing the entire threat landscape, to mitigate the risk of working in silos. A threat-agnostic approach addresses these findings directly, providing critical cross-cohort insight into intersectional vulnerability and polycriminality.
Why does this deliver precision to CSE? The Casey Audit makes clear that CSE is underreported: victims frequently did not report because they did not believe they were being abused, feared the consequences, or were terrified of being criminalised for crimes their abusers had involved them in. When hidden harm crimes are underreported, a threat-agnostic approach maximises the value of the intelligence that you hold. Automating the entire threat landscape reveals opportunities that can backfill any lack of tactical options for CSE. For example, drugs, money and gifts obtained through criminal enterprise are commonly used to entice and coerce vulnerable children into sexual exploitation. Tactics resulting in arrest or imprisonment of exploitative adults for drugs, money laundering or acquisitive crime can therefore prevent or reduce some group-based CSE.
While threat-agnosticism increases the tactical options available for police, true early intervention requires a multiagency public health approach with partners who hold direct relationships with vulnerable children.
Navigate existing pathways to improve partnership working
Recommendation 5 of the Casey Audit advocates for mandatory, enforceable sharing of information related to CSE between all statutory safeguarding partners. The government has accepted this, and provisions in the Children’s Wellbeing and Schools Bill will introduce a new duty to share information where it is necessary to safeguard children. Ahead of the new duty, Approved Professional Practice from the College of Policing already details existing legal frameworks for sharing information.
For the last decade, the discipline of Contextual Safeguarding, pioneered by Prof. Carlene Firmin at the Universities of Bedfordshire and Durham, has already equipped partners to intervene with peer groups of children at risk of CSE. The requirement for a Contextual Safeguarding approach is referenced throughout the Families First Partnership Programme Guide, and the discipline is already embedded in existing structures such as Violence Reduction Units, Multiagency Safeguarding Hubs and Community Safety Partnerships.
While i2 has several technologies that support information sharing, the challenge is as much cultural as it is legal and technological. At the 2025 Contextual Safeguarding conference, partners in Children’s Social Care, Education and the third sector rightly expressed concern about the criminalisation and surveillance of children, dehumanising quantitative approaches, and disproportionate interventions for minority communities. If these concerns are not addressed, there is a risk of a widening cultural rift as the NPCC National Policing Digital Strategy (2025–2030) drives increased automated prioritisation. Against a backdrop of scrutiny over police technology procurement, the consequences of deploying automated solutions without a detailed understanding of partnership working may include a risk to public and partnership trust and the principle of policing by consent.
i2 therefore advocates for careful co-design of partnership processes. Technology should provide signposts towards a proportionate, nuanced appreciation of contextual risk — as opposed to enforcement-only tasking to a list, score or quota. i2’s principles are grounded in evidence-based best practice, as demonstrated by our Academic Programme. This equips us to observe the cultural differences between police and partnership evidence bases – as well as potential synergies when these contrasts are rigorously addressed. We strongly support any work that builds bridges between agencies, as this is foundational to a multiagency public health approach.
The same data environments that enable the identification and disruption of CSE also generate a secondary challenge: the exploitation of public concern for political purposes. 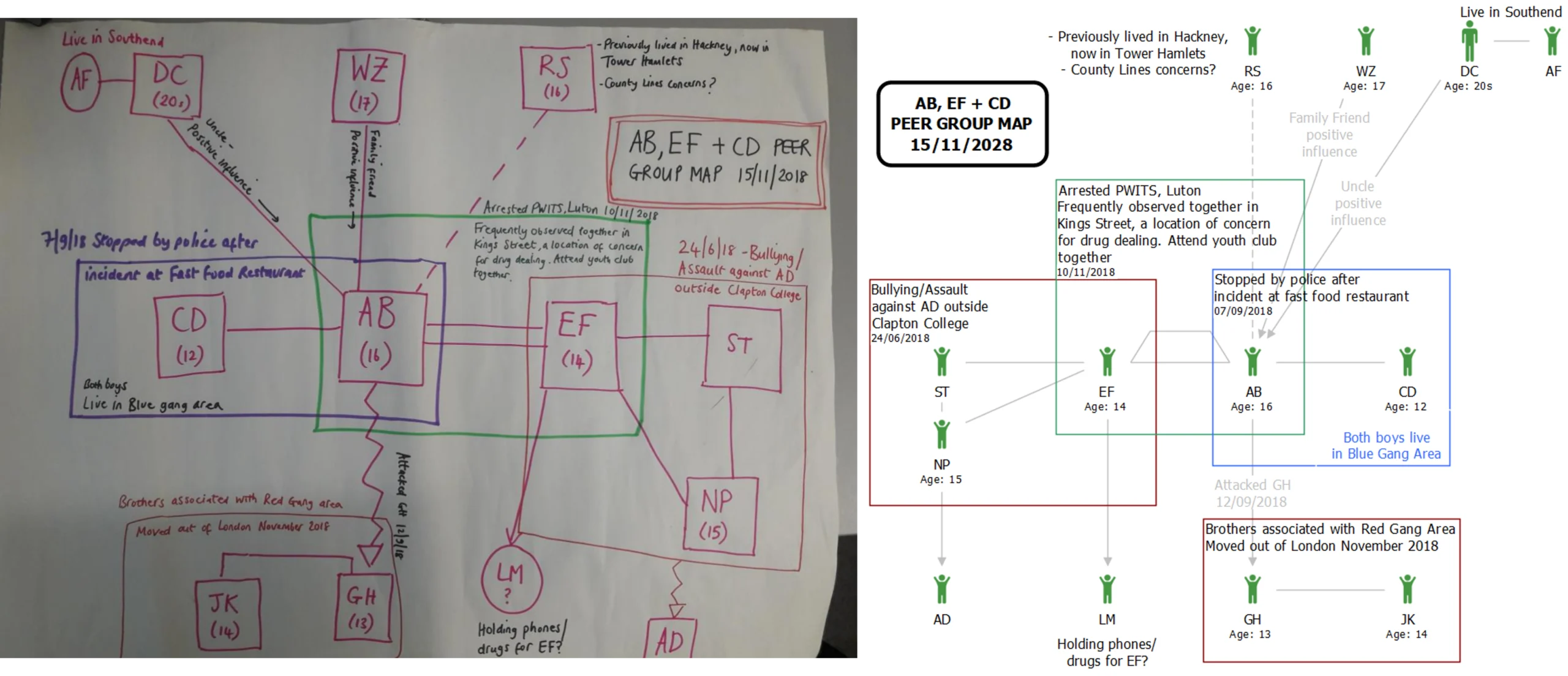
The illustration above shows a chart taken from the Contextual Safeguarding Network’s Peer Group Mapping Guidance, alongside the same chart rebuilt in i2 Analyst’s Notebook, demonstrating highly compatible notation affordances.
Achieve insight into the community tensions that can accompany CSE
The Casey Audit highlights that the concept of “grooming gangs”, while used by parts of the public and captured in media reporting, is not captured clearly in any official data set. Ambiguous categories lead to ambiguous operational outcomes. Ambiguities can also be exploited.
The technological landscape of 2026 requires no human to be in this exploitation loop. Automated trawling of the internet can identify suspects who fit predefined profiles that serve a political agenda; large language models can automate outrage content; and bots amplify it on social media using astroturfing tactics to create a false impression of virality. Within hours, a single news story can become amplified by state and non-state actors whose agenda typically omits the findings of Operation Yewtree, or the current Epstein investigations, in selecting which children are at risk and which adults pose a threat. The consequences of this can damage democracy.
i2 partners with data providers, providing on-demand access to online sources such as social media. This provides threefold capability — to investigate the growing threat of online exploitation, monitor community tensions, and understand the spread of online disinformation.
Next Steps: Achieving More with What You Already Have
The Casey Audit’s 12 recommendations have all been accepted by government. The Independent Inquiry into Grooming Gangs formally begins this month, in April 2026. Operation Beaconport is reviewing hundreds of previously closed cases. The HMICFRS progress inspection found encouraging signs but also identified remaining gaps in problem profiling and data quality.
The capabilities described in this article are not aspirational. They are already available under existing licenses, deliverable by existing analysts with appropriate training and assurance, and aligned with the evidence base that the Casey Audit, HMICFRS, the College of Policing and the NIM Landscape Review have established.
Every UK constabulary already has access to i2 software under the BlueLight Commercial Access for All Agreement.
If you would like to explore how these capabilities can support your force’s response to the Casey Audit and the wider CSE landscape, contact us.
This article discusses analytical capabilities in the context of published and public reports. It does not suggest endorsement by, involvement in, or influence over any live investigation, inquiry, or judicial process. Operational decisions remain the responsibility of individual agencies, subject to local governance, safeguarding duties, and applicable law.
Category: Advertorial
Advertisement
Job of the week
Regional/Country Security Advisers

- Foreign, Commonwealth & Development Office
- Overseas, and we anticipate roles arising within 12 months of the interviews in locations such as Nairobi, Maputo, Karachi, Cairo, Tunis and Riyadh.
- £38,500 per annum
We lead the UK’s diplomatic, development and consular work around the world. We employ around 17,000 staff in our global network of 281 offices worldwide. Our UK-based staff work in King Charles Street in London, Abercrombie House in East Kilbride and in Milton Keynes.
Read more

